Picture the most bothersome, invasive digital spam you’ve come across. In all possibility, you’re thinking about undesirable e-mails. These can be discouraging, however they are certainly not the only kinds of spam.
In truth, spam can strike every digital existence possible, varying from blog sites to social networks. And yes, it stays a substantial issue for e-mail, where it obstructs of genuine interactions in between people and organizations that can in fact include worth to their lives. No matter where this happens or which kinds of spam are used, it’’ s essential to comprehend the risks it postures — – and how it can be avoided.
.How spam overthrows our digital lives.
All kinds of spam are frustrating to get on an individual level, however that is far from the only concern it requires. From a marketing point of view, spam is bothersome because it disrupts efficient relationships in between customers and the companies in which they reveal genuine interest.
With e-mail, this manifests in exceedingly strong scrap filters that avoid clients from getting newsletters or other asked for interactions. In other places, spam sidetracks users from sites, social networks posts, or other material from which they might otherwise acquire noticeable worth.
This can be both destructive and frustrating from a security viewpoint. The links consisted of within spam e-mails or posts might lead to infections or other dangers.
The excellent news? While lots of people take it for given that spam will completely become part of their digital lives, this does not really need to hold true. When we recognize spam and acknowledge all the scenarios in which it can appear, it’s possible to take targeted actions to eliminate it without likewise prohibiting helpful material such as preferred marketing e-mails.
To assist, we’ve highlighted a few of the most considerable kinds of spam listed below.
.Email spam.
To start, we will look into the kind of web spam you are most likely most acquainted with: unsolicited e-mails. These are a familiar yet dreadful sight in the majority of inboxes. While innovative filters obstruct most of these e-mails, some still handle to make it through.
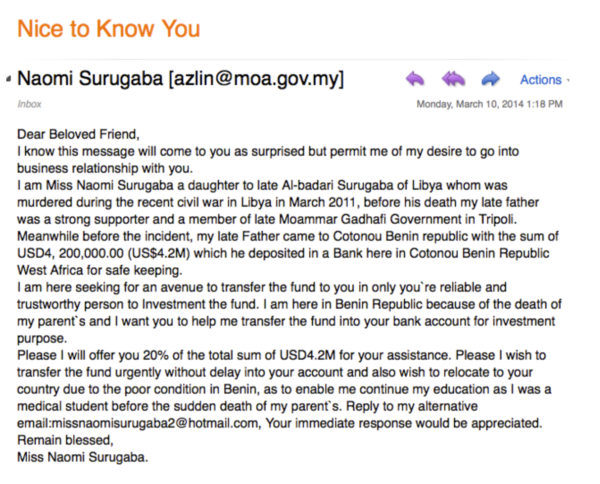 Email spam is not just frustrating to get however likewise possibly unsafe if it includes phishing. Image source: Mother Jones
Email spam is not just frustrating to get however likewise possibly unsafe if it includes phishing. Image source: Mother Jones
Surprisingly enough, current reports recommend that e-mail spam is presently experiencing a stable and sluggish decrease. According to information from cybersecurity business Kaspersky , spam represented 55.76% of overall e-mail in January 2020 (compared to 48.16% by June of that year). Regardless of the constant decline in spam, it stays a substantial issue — – even offered Gmail’s claims of obstructing 10 million destructive and spam e-mails per minute.
Email spam is remarkably varied. It runs the range from slightly bothersome to actively threatening to those who get it —– and even to other individuals on their contact lists. Typical examples of spam e-mails consist of the following:
.Phishing: If you’ve ever been gotten in touch with by a spammer impersonating a genuine individual or service, you’ve been targeted in a phishing attack . The objective is to persuade you that the sender really exists which you will in some way take advantage of sharing delicate information such as your Social Security number or charge card information.Baiting: Similar to phishing, this method might be more appealing to targeted victims because it includes the guarantee of a benefit. This might take the kind of totally free downloads or memberships. Lots of otherwise careful users will gladly quit delicate details in exchange for such freebies.Antispam spam: This name may appear complicated, however the principle behind it is basic —– lots of spammers declare to supply options that secure their prospective target versus other sources of spam. Rather, nevertheless, e-mail receivers might be sent out accessories including links or infections to hazardous pages.Messenger spam.
Similar in numerous aspects to kinds of spam connected to email, messenger spam straight strikes messaging services on sites such as Facebook, Instagram, and LinkedIn. These spam messages can frequently be classified likewise to the most typical spam e-mails. They might be harder to filter, nevertheless, and are most likely to reach users who invest more time on social networks than examining their e-mail inboxes.
Phishing and baiting are especially typical, with some messages likewise consisting of harmful software application. These messages might contaminate computer systems or mobile gadgets if opened. Some might even trigger Facebook fans and good friends to get completely or undesirable hazardous messages.
.Remark spam.
If you’ve ever experienced an abundance of random, unimportant talk about your site’s post, the source might be a ruthless remark spammer. This kind of spam includes web-based kinds, such as those discovered within blog-based remark areas or on neighborhood online forums.
Sometimes described as “spomment,” remark spam generally includes some sort of reply that is certainly unimportant to a provided blog site or online forum thread’s primary subject, along with a link that causes the spammer’s site.
Comment spam can likewise include social networks platforms, where it strikes the remark areas for picture and video uploads, in addition to easy status updates. With social networks, spam can discover its method onto personal specific pages and groups, in addition to business-oriented pages and even promoting efforts.
.Trackback spam.
As a particular kind of remark spam, this issue takes place when trackbacks are utilized to excess. Prior to you can genuinely comprehend this type of spam, nevertheless, it’s essential to master the idea of the trackback: an alert that signals other sites that you have actually connected to them. Utilized properly, this method can lead to backlinks.
Unfortunately, when trackbacks are made it possible for, other websites can connecting to your page. This in turn indicates that they are connected within the remark area. When top quality sites are included in trackbacks however bothersome if spammers send out links to harmful sites by method of remarks, this can be beneficial.
.Internet browser spam.
Although less typical than e-mail or messenger-oriented kinds of spam, web browser spam strikes far a lot of unwary users. These rip-offs make use of the increasing appeal of web browser alerts, which, when utilized appropriately, can enhance digital interactions to restrict the requirement for open tabs. These can likewise be controlled to develop considerable security risks.
Unfamiliar to lots of targets, this kind of spam includes internet browser notices, which deceive receivers into signing up for bothersome sites. These bombard users with notices associated with unpleasant plans. A number of today’s leading computer system and mobile security options are incapable of spotting and getting rid of these notices, so they are typically able to continue unattended.
.Unfavorable SEO.
The black-hat techniques highlighted above are not simply irritating from a user experience viewpoint, however they’re troublesome from the viewpoint of seo (SEO). You’ve striven to carry out a material technique that includes mindful keyword choice and link structure, however the outcomes will be restricted if you’re regularly weakened by spammers that litter your website or social networks pages with low-grade material and links.
Unfortunately, some celebrations take this idea to the next level by actively attempting to hinder your SEO efforts. Called unfavorable SEO, this black-hat method includes dishonest methods that intend to undermine your positioning in online search engine rankings. This takes a range of types, with typical examples consisting of:
.Eliminating top quality backlinks by sending out web designers phony elimination requestsForming spammy links that cause the targeted business’s websiteCreating social media or phony evaluations profiles with completion objective of triggering reputational damageDeveloping replicate variations of site material.
Negative SEO attacks can be challenging to identify as the taking place damage might develop over a substantial amount of time. In some cases, nevertheless, efficiency concerns at first credited to unfavorable SEO really stem from errors on the having a hard time site’s end.
.How to safeguard your site and marketing projects from spam.
As you can see, spam can originate from a large range of sources and can frequently be hard to find. Efforts to avoid spam should be detailed. There is no single tool or method that can entirely get rid of spam, however a well-rounded method can obstruct the most typical circumstances of it from your various sites, e-mail projects, and social networks platforms.
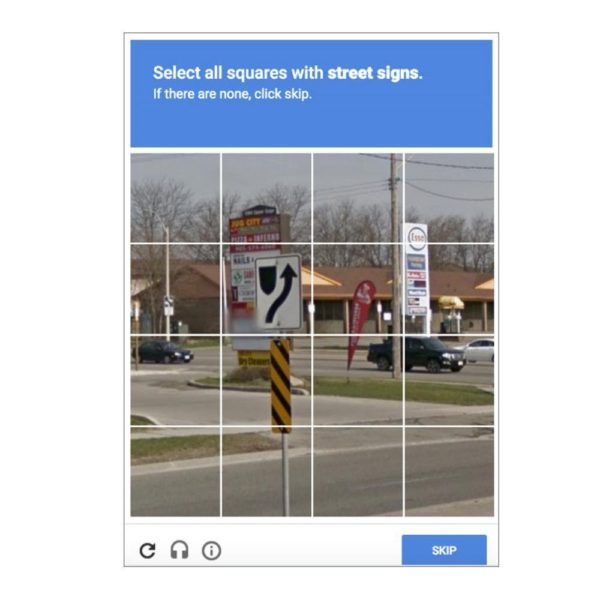 ReCAPTCHA can be an important alternative for enhancing user experience while restricting spam.
ReCAPTCHA can be an important alternative for enhancing user experience while restricting spam.
The leading services for reducing and avoiding spam consist of:
. Evaluating and safeguarding backlinks: If you’re targeted by an unfavorable SEO attack, you can utilize innovativetools to identify who is constructing links to your website– or whether you’ve just recently lost essential backlinks. Secure the most important backlinks by utilizing domain e-mail addresses and —, naturally, keeping an eye on these links carefully.Opting for CAPTCHA kinds: While these can not find all kinds of remark spam (such as manual variations, in which human beings change spambots to send kinds including hazardous links), they stay an efficient service for avoiding spam overload. If benefit is an issue, attempt Google’s reCAPTCHA instead.Using honeypots: A leading tool for restricting spam, honeypots are perfect because they do not trouble users to the very same degree as CAPTCHA. These usually include information that seems important to prospective spammers however is really planned to capture them and ideally evaluate their attacks. Ditch spam and bad star techniques for excellent.
Equipped with your newly found understanding of the numerous kinds spam can take, you can utilize proactiveservices such as CAPTCHA, honeypots, and backlink defense to restrict its influence on your digital marketing project. As spam vanishes, the outcome will be a more powerful connection with, and more trust from, genuine leads.
.
To discover more about genuine marketing techniques that construct authentic relationships with potential customers, have a look at The Download — your guide to all elements of internet marketing.
.
The post Types of Spamming appeared initially on Constant Contact .
.
Read more: blogs.constantcontact.com
